- News
- Business News
- India Business News
- Why you need to be cautious when you draw cash at ATM
Trending
This story is from August 1, 2016
Why you need to be cautious when you draw cash at ATM
In March, fraudsters in Ahmedabad withdrew as much as Rs 31.93 lakh using various debit cards in 146 transactions from different cities, including Mumbai, and Chennai. The fraudsters modus operandi was to make the ATM dispense without the bank server recording the malfunction.

In March, fraudsters in Ahmedabad withdrew as much as Rs 31.93 lakh using various debit cards in 146 transactions from different cities, including Mumbai, and Chennai. The fraudsters modus operandi was to make the ATM dispense without the bank server recording the malfunction.
In this instance, malware, a favourite with ATM hackers, can gain access to the ATM's operating system and make the machine spit out cash.
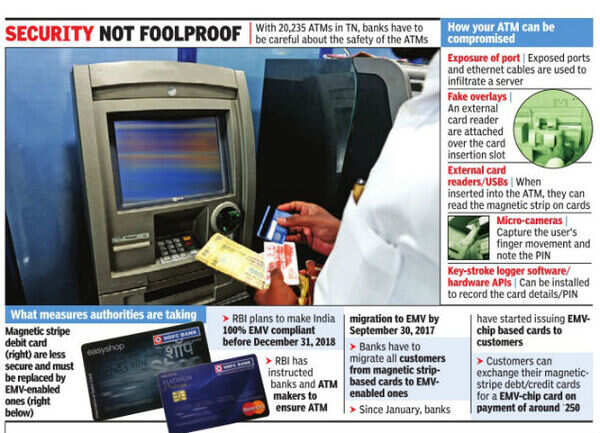
“Our ATMs are susceptible to hacks. Many times I have spotted ATMs with their ethernet and hub exposed. This is an invitation to fraudsters to connect to the ATM using their mobile or laptop,“ says Vinod Senthil, ethical hackers and founder of InfySec.
As customers, the amount of losses can be mitigated to an extent by setting caps on the spending limit, number of transactions in a day, or geographical limit from where cash is withdrawn. While some banking apps allow this kind of customization, most banks have a restriction on overseas transactions, which helps in preventing online fraud attempts from abroad. But such measures cannot assure security.
Banking fraud in Tamil Nadu, including ATM breaches, nearly tripled to Rs 1,831.08 crore in 2014-15 from the previous year. The state with the second largest ATM network, has seen a fair share of fake overlays, malware, data breaches and circuit breakers compromising its network of ATMs, switches and bank servers.
Fake overlays on ATMs are another weak point in the chain of bank security. “Earlier there were overlays which were small attachments near the dispensation slot. Now fraudsters have become so ingenious that they create a large overlay, the entire length and breadth of the ATM, which is undetectable by a lay person,“ says Srikumar V of ATM-maker Diebold.
“Apart from the fake overlay , which is embedded with a card reader, fraudsters also position a tiny camera. The camera captures the finger movement of ATM users, so that the PIN can be read,“ says Puneet read,“ says Puneet Kapoor, senior executive vice-president of Kotak Mahindra Bank.
ATM breaches can also occur, when hackers break into the bank's ATM s switch. “Before cash is dispensed, there are multiple messages being sent back and forth within nano seconds between the ATM bank and the sender receiver bank, which could be the same or different. One message confirms whether there is money in the account for cash dispensation, and after the cash gets dispensed the message on the action goes back to the user's bank. This is where a circuit breaker is employed,“ says Senthil. “As soon as the cash is dispensed the signal gets disconnected and the user's bank assumes a transaction failure, when it is actually not so.“ With such data breaches, thousands of card details could be compromised.
End of Article
FOLLOW US ON SOCIAL MEDIA